Hacks in the DeFi ecosystem
- Market maker Wintermute was drained of $160 million, after falling prey to a DeFi exploit.
- A white hat hacker uncovered a multi-million dollar vulnerability in the Ethereum Arbitrum Nitro bridge and received 400 ETH as payout.
- 90 assets were hit by the Wintermute attack, none of the assets were over notional $2.5 million, no major sell-off expected.
Exploits in the DeFi ecosystem, on decentralized exchanges, market makers and bridges have become increasingly common. Wintermute was drained of $160 million in the latest exploit, but its CEO has confirmed on-chain trading will continue. Ethereum and Arbitrum-Nitro bridge dodged a multi-million dollar attack, paying out 400 ETH to a white hat hacker.
Also read: Bitcoin price: All eyes on FOMC, negative inflation could slash hopes for crypto
Wintermute suffers $160 million exploit, no major sell-off expected
Leading crypto market maker Wintermute was hit by a $160 million exploit. Wintermute has partnered with the world’s best crypto exchanges and projects to provide liquidity. Therefore an exploit on Wintermute raised several concerns among the crypto community.
Evgeny Gaevoy, the CEO of Wintermute pointed out that the DeFi wing of the firm was targeted in the attack and funds in the centralized exchange and over-the-counter offerings remained safe.
Among the 90 assets hit by the attack, only two have been for notional over $1 million and none more than $2.5 million. Gaevoy assured the community that there will be no major sell-off in the crypto ecosystem. The CEO shed light on the firm’s solvency. “Insolvency” is a common term that has been making the rounds in the crypto market since Three Arrows Capital fund’s failure.
Gaevoy assured traders that Wintermute is still solvent. He was quoted as saying:
We are solvent with twice over that amount in equity left. If you have a MM agreement with Wintermute, your funds are safe. There will be a disruption in our services today and potentially for the next few days and will get back to normal after. We are (still) open to treating this as a white hat, so if you are the attacker – get in touch.
An address associated with the Wintermute hack (0xe74b28c2eae8679e3ccc3a94d5d0de83ccb84705) deposited a whopping $114 million into Curve. The address has been flagged on Etherscan as related to the Wintermute exploit.
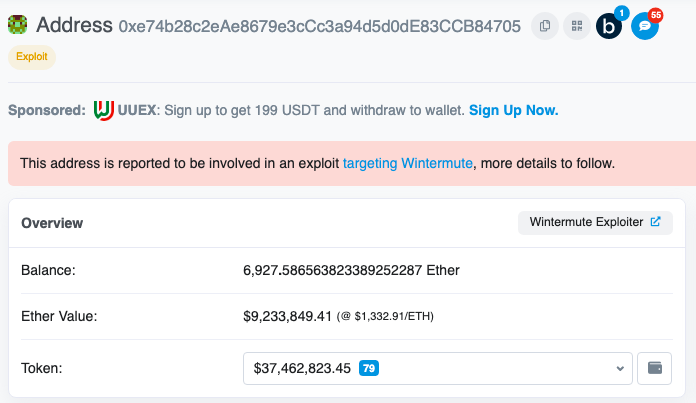
Wintermute hacker address

$114 million added to Curve
Gaevoy shared updates on the exploit, attributing it to human error. The market maker has put a 10% bounty to the hacker if all funds are returned, approximately 16 million USDC. The attack vector was associated with the market maker’s Ethereum vault, used for on-chain DeFi trading operations and this is separate from CeFi and OTC operations of the firm.
Short communication on the ongoing Wintermute hack
— wishful cynic (@EvgenyGaevoy) September 20, 2022
None of Wintermute’s CeFi or OTC wallets were affected or compromised and the exploit was most likely a “Profanity-type exploit.”
Profanity, used for key-generation on the compromised wallet address was exploited last week according to 1inch contributors and the hack was therefore a human error. Despite the discovery of the Profanity exploit, the firm failed to switch its key generation from the compromised project to elsewhere.
White hat hacker identified huge vulnerability in Ethereum to Arbitrum bridge
A white hat hacker uncovered a multi-million dollar vulnerability in the bridge linking Ethereum and Arbitrum. Arbitrum is a layer-2 optimistic rollup solution for Ethereum. It reduces network congestion and saves fees. Arbitrum Nitro aims to simplify communication between Arbitrum and Ethereum.
The hacker received a 400 ETH bounty for the find. The attacker goes by the name: Riptide. Riptide explained the exploit in a Medium post. The post reads:
We could either selectively target large ETH deposits to remain undetected for a longer period of time, siphon up every single deposit that comes through the bridge, or wait and just front-run the next massive ETH deposit.
If a hacker with malicious intent identified the vulnerability the hack could potentially drain tens or hundreds of millions worth of Ethereum. 168,000 ETH, valued over $225 million could have been stolen in the exploit.
As there was massive earning potential from the exploit, Riptide believes the find should be eligible for a max bounty, worth $2 million.